Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You recently discovered that the developers at your company emailed Azure Storage Account keys in plain text to third parties.
You need to ensure that when Azure Storage Account keys are emailed, the emails are encrypted.
Solution: You configure a mail flow rule that matches a sensitive info type.
Does this meet the goal?
You are configuring a data loss prevention (DLP) policy to report when credit card data is found on a Microsoft Entra joined Windows device.
You plan to use information from the policy to restrict the ability to copy the sensitive data to the clipboard.
What should you configure in the policy advanced DLP rule?
You have a data loss prevention (DLP) policy configured for endpoints as shown in the following exhibit.
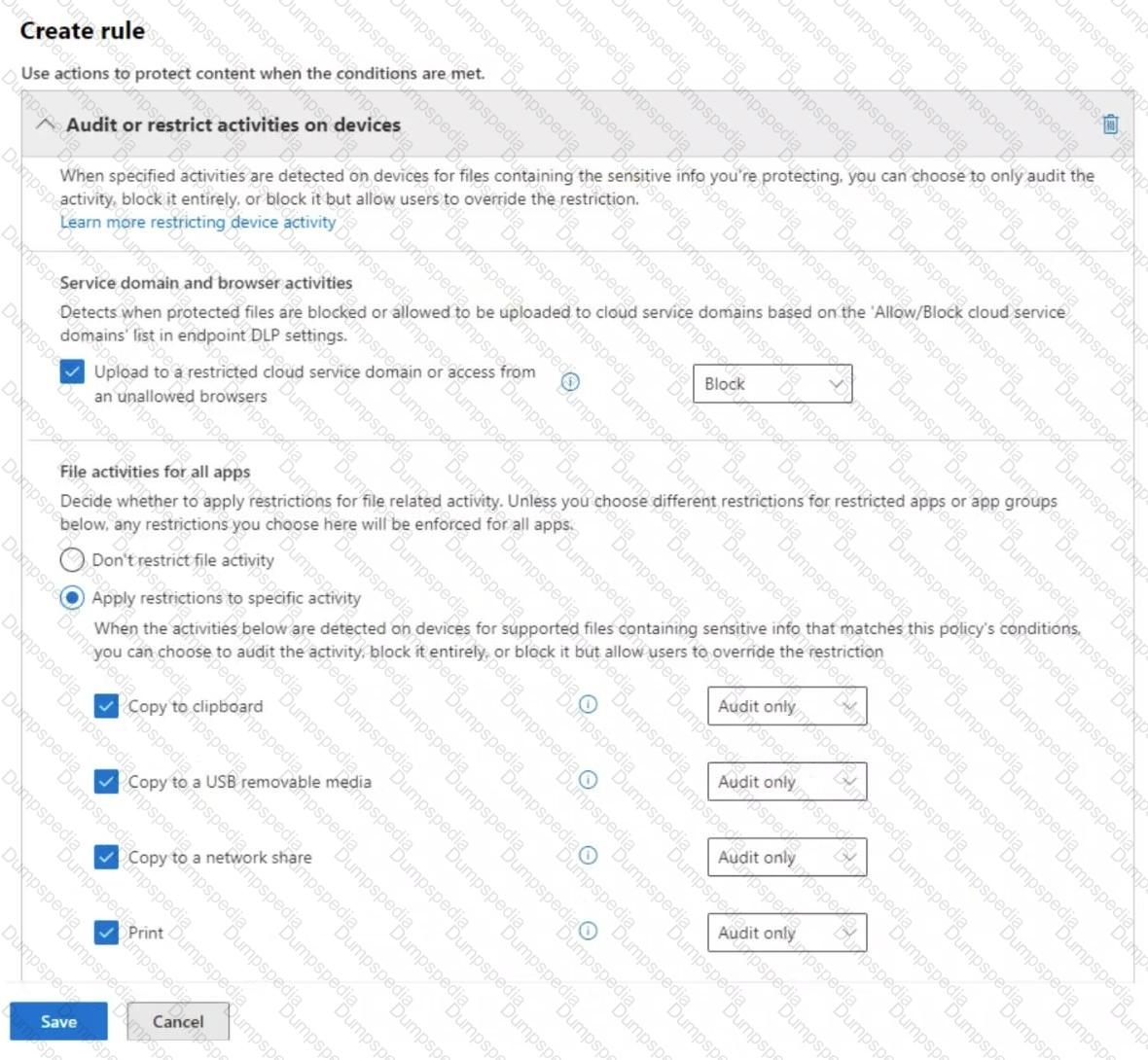
From a computer named Computer1, a user can sometimes upload files to cloud services and sometimes cannot. Other users experience the same issue.
What are two possible causes of the issue? Each correct answer presents a complete solution.
NOTE : Each correct selection is worth one point.
You have a Microsoft 365 ES subscription.
A security manager receives an email message every time a data loss prevention (DIP) policy match occurs. You need to limit alert notifications to actionable DLP events. What should you do?
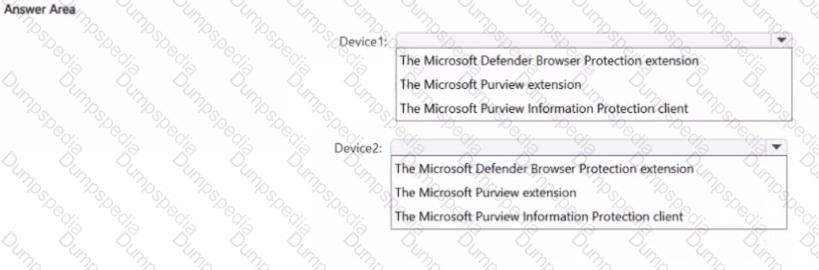
You have a Microsoft 36S ES subscription that contains two Windows devices named Devicel1and Device2 Device1 has the default browser set to Microsoft Edge. Devke2 has the default browser set to Google Chrome.
You need to ensure that Microsoft Purview insider risk management can collect signals when a user copies files to a USB device by using their default browser.
What should you deploy to each device? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription.
You plan to implement insider risk management for users that manage sensitive data associated with a project.
You need to create a protection policy for the users. The solution must meet the following requirements:
● Minimize the impact on users who are NOT part of the project.
● Minimize administrative effort.
What should you do first?
You implement Microsoft 36S Endpoint data loss pi event ion (Endpoint DIP).
You have computers that run Windows 11 and have Microsoft 365 Apps instated The computers are joined to a Microsoft Entra tenant.
You need to ensure that Endpoint DIP policies can protect content on the computers.
Solution: You onboard the computers to Microsoft Defender for Endpoint.
Does this meet the goal?
You have a Microsoft 365 E5 tenant that uses a domain named contoso.com.
A user named User 1 sends link based, branded emails that are encrypted by using Microsoft Purview Advanced Message Encryption to the recipients shown in the following table.
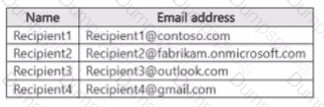
For which recipients Can User1 revoke the emails?
You have a Microsoft 365 E5 subscription that contains the sensitive information types (SITs) shown in the following table.
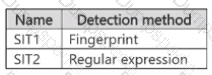
You plan to create the policies shown in the following table and assign them to a Microsoft SharePoint Online site.
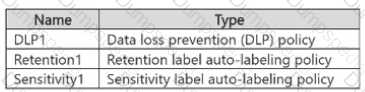
Which policies can use SIT1. and which policies can use SIT2? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription.
You need to ensure that encrypted email messages sent to an external recipient can be revoked or will expire within seven days.
What should you configure first?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 subscription.
You have a user named User1. Several users have full access to the mailbox of User1.
Some email messages sent to User1 appear to have been read and deleted before the user viewed them.
When you search the audit log in the Microsoft Purview portal to identify who signed in to the mailbox of User1, the results are blank.
You need to ensure that you can view future sign-ins to the mailbox of User1.
Solution: You run the Set-MailboxFolderPermission -Identity " User1 " -User User1@contoso.com -AccessRights Owner command.
Does that meet the goal?
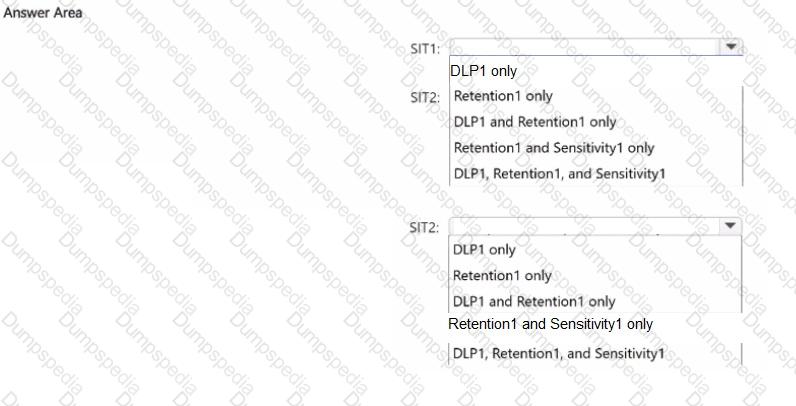
You have a Microsoft 365 E5 subscription.
You have a file named Customer.csv that contains a list of 1,000 customer names.
You plan to use Customer.csv to classify documents stored in a Microsoft SharePoint Online library.
What should you create in the Microsoft Purview portal, and which type of element should you select? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
HOTSPOT
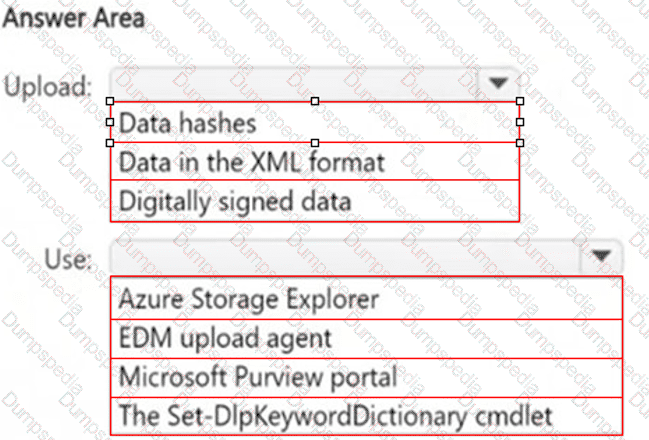
You plan to create a custom sensitive information type that will use Exact Data Match (EDM).
You need to identify what to upload to Microsoft 365, and which tool to use for the upload.
What should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
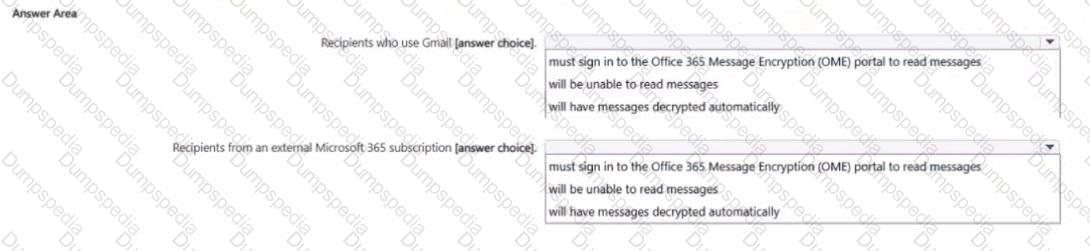
You have a Microsoft 36S subscription.
In Microsoft Exchange Online, you configure the mail flow rule shown in the following exhibit.
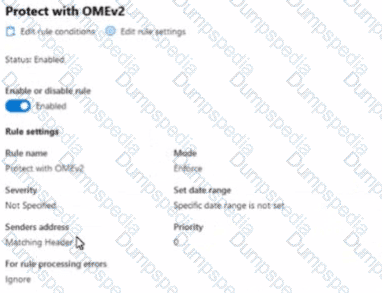
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
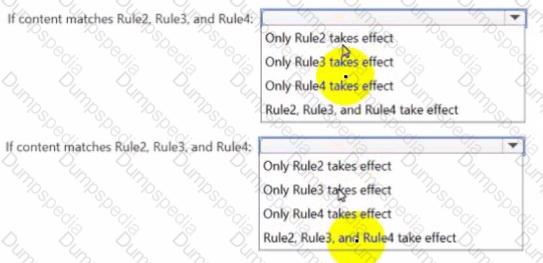
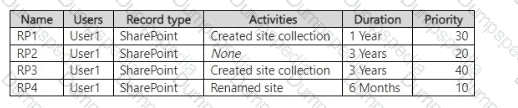
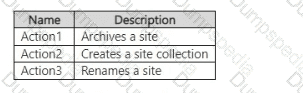
You have a data loss prevention (DIP) policy that has the advanced DIP rules shown in the following table.
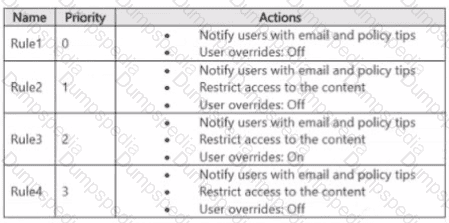
You need to identity which rules will apply when content matches multiple advanced DIP rules.
Which rules should you identify? To answer, select the appropriate options in the answer area.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant and 500 computers that run Windows 11. The computers are onboarded to Microsoft Purview.
You discover that a third-party application named Tailspin_scanner.exe accessed protected sensitive information on multiple computers. Tailspin_scanner.exe is installed locally on the computers.
You need to block Tailspin_scanner.exe from accessing sensitive documents without preventing the application from accessing other documents.
Solution: From the Microsoft Defender for Cloud Apps, you mark the application as Unsanctioned.
Does this meet the goal?
You have a Microsoft 365 E5 subscription. The subscription contains 500 Windows devices that are onboarded to Microsoft Purview.
You need to prevent users from sharing sensitive information with third-party generative Al websites. Which Microsoft Purview solution should you use?
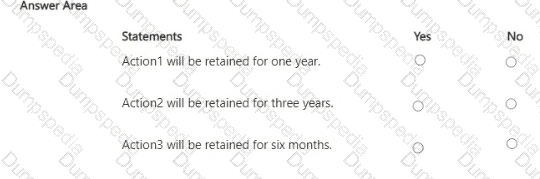
You have a Microsoft 365 E5 subscription that uses Microsoft Purview Audit (Premium) with the 10-Year Audit Log Retention add-on license.
The subscription contains the audit retention policies shown in the following table.
From the SharePoint Online admin center, User1 performs the actions shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE; Each correct selection is worth one point.
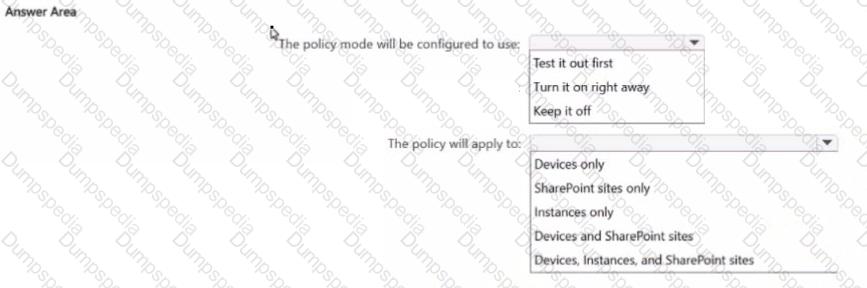
You have a Microsoft 36S ES subscription.
From the Microsoft Purview Data Security Posture Management for Al portal, you review the recommendations for Al data security
You plan to create a one-click policy to block elevated risk users from pasting or uploading sensitive data to Al websites
How will the policy be configured? To answer, select the appropriate options in the answer area
NOTE: Each correct selection is worth one point.
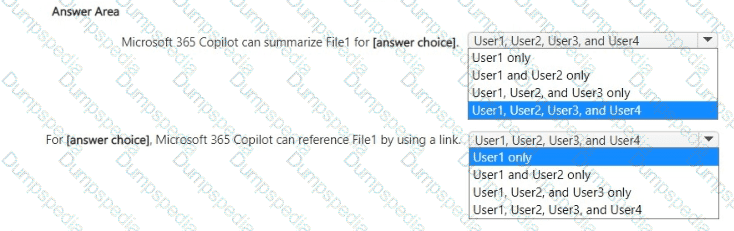
You have a Microsoft 365 E5 subscription that contains four users named User1, User2, User3, and User4 and a file named File1.docx.
To File1, you apply a sensitivity label that has the permissions shown in the following exhibit.
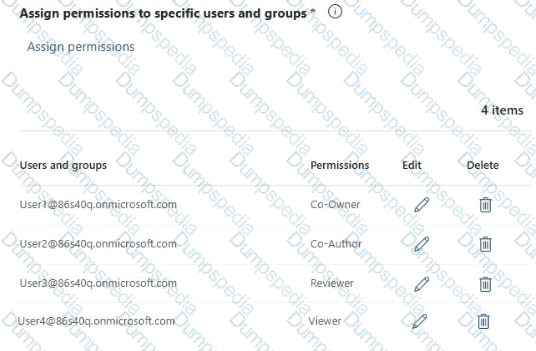
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE; Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that contains the adaptive scopes shown in the following table.
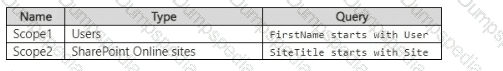
You create the retention policies shown in the following table.
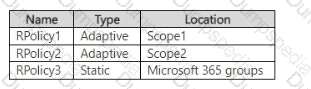
Which retention policies support a preservation lock?
You have a Microsoft J65 ES subscription.
You need to create a Microsoft Defender for Cloud Apps policy that will detect data loss prevention (DIP) violations. What should you create?
HOTSPOT
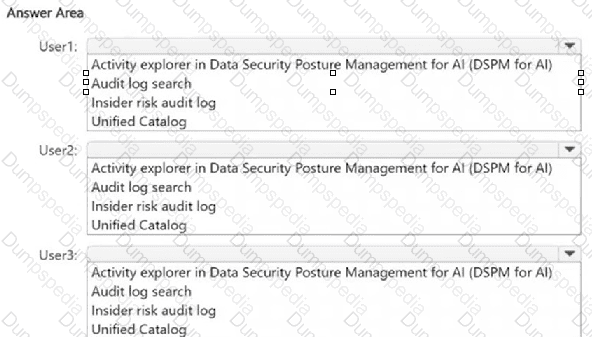
You have a Microsoft 365 E5 subscription. The subscription contains devices that are onboarded to Microsoft Purview and configured as shown in the following table.
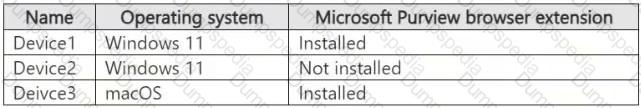
The subscription contains the users shown in the following table.
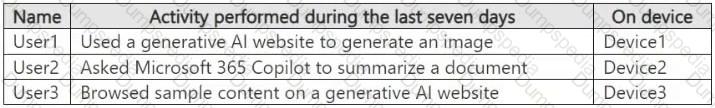
You need to review the activities.
What should you use for each user? To answer, select the appropriate options in the answer area.
NOTE : Each correct selection is worth one point.
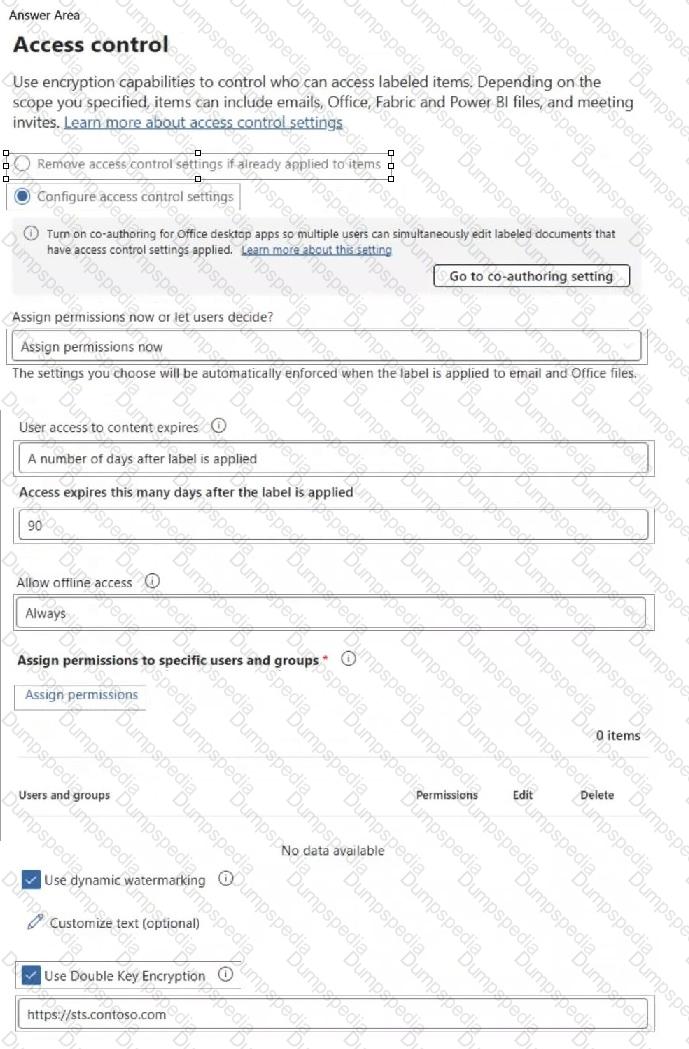
You have a Microsoft 365 E5 tenant that contains a sensitivity label named label1.
You plan to enable co-authoring for encrypted files.
You need to ensure that files that have label1 applied support co-authoring.
Which two settings should you modify? To answer, select the settings in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 36S ES subscription
You plan to create an met data match (EDM) classifier named EDM1.
You need to grant permissions to hash and upload the sensitive ^formation source table for EDMI. What should you create first?
HOTSPOT
You have a Microsoft 365 E5 subscription.
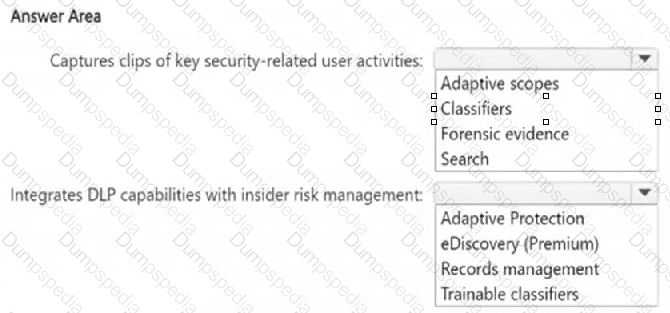
You need to implement a compliance solution that meets the following requirements:
● Captures clips of key security-related user activities, such as the exfiltration of sensitive company data.
● Integrates data loss prevention (DLP) capabilities with insider risk management.
What should you use for each requirement? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that contains a Microsoft SharePoint Online site named Site1. Site1 contains the files shown in the following table.
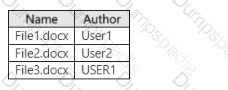
In the Microsoft Purview portal, you create a content search named Conlent1 and configure the search conditions as shown in the following exhibit.
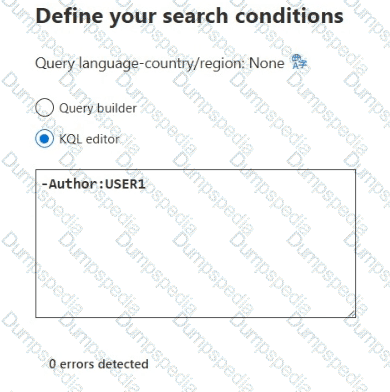
Which files will be returned by Content1?
HOTSPOT
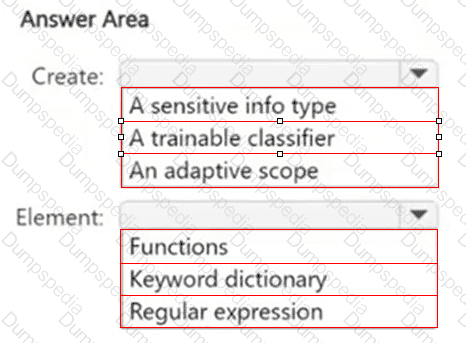
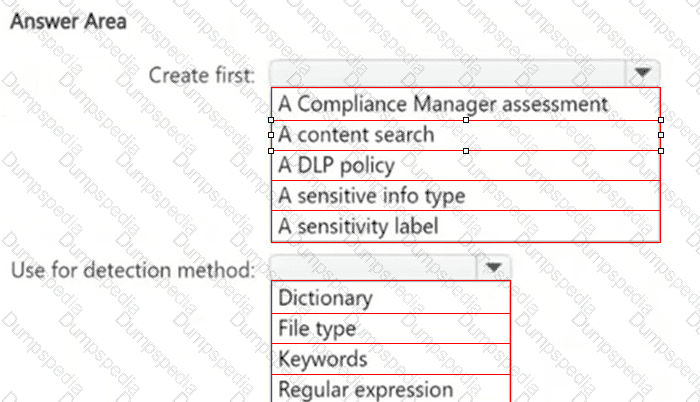
You need to meet the technical requirements for the confidential documents.
What should you create first, and what should you use for the detection method? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
HOTSPOT
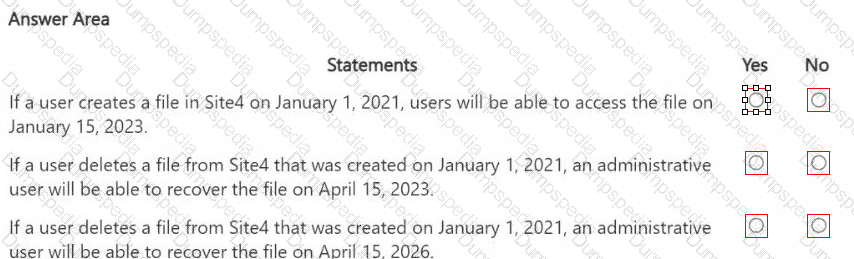
You are reviewing policies for the SharePoint Online environment.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You need to meet the technical requirements for the creation of the sensitivity labels.
To which user or users must you assign the Sensitivity Label Administrator role?
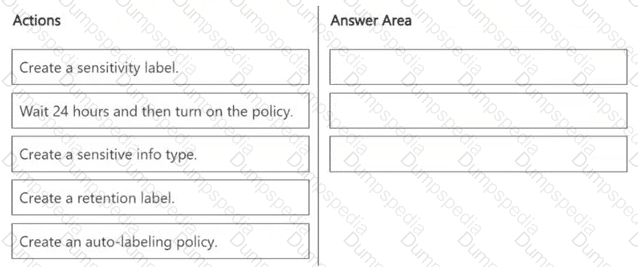
You need to meet the technical requirements for the Site1 documents.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to meet the retention requirement for the users ' Microsoft 365 data.
What is the minimum number of retention policies required to achieve the goal?
HOTSPOT
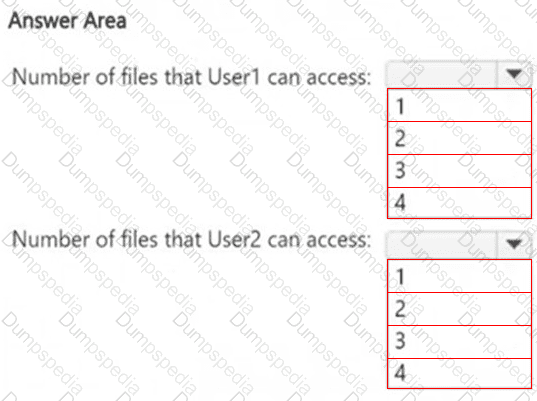
How many files in Site2 can User1 and User2 access after you turn on DLPpolicy1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.